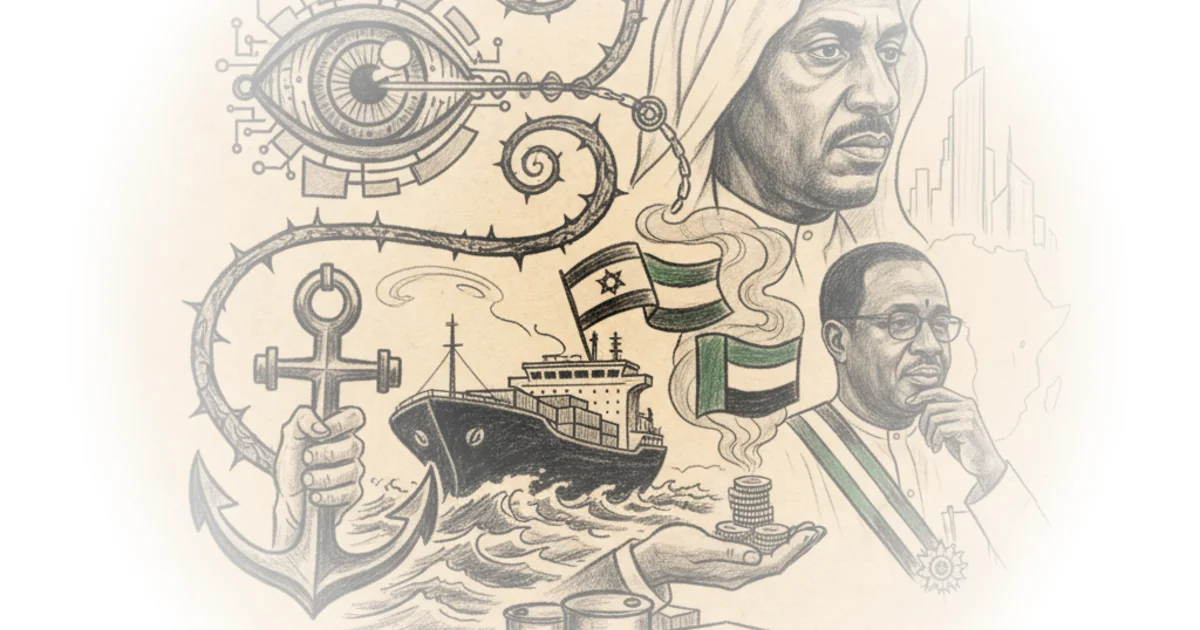
This piece by Ryan Grim & Jeremy Scahill exposes a chilling architecture where counter-terrorism rhetoric served as a Trojan horse for surveillance capitalism and resource extraction. By unearthing a trove of emails, the authors reveal how a network of billionaires and former intelligence officials transformed the chaos of the Boko Haram insurgency into a lucrative testing ground for biometric technologies first deployed against Palestinians. This is not merely a story about a deceased financier; it is an investigation into how the "security industrial complex" monetizes human suffering to secure energy and logistics dominance in West Africa.
The Architecture of Chaos
Ryan Grim & Jeremy Scahill construct their argument around a disturbing continuity: the same technologies used to manage populations in occupied territories were repurposed for African ports and universities. The authors detail how Jeffrey Epstein, often dismissed as a lone predator, was actually a central node in a global network connecting the United Arab Emirates, Israel, and Nigeria. They write, "Epstein was keen to profit from armed conflicts on the African continent," a sentence that reframes his entire career from a pedophile financier to a geopolitical broker of instability.
The coverage meticulously traces how Ehud Barak, the former Israeli Prime Minister, leveraged the fear of Boko Haram to introduce Israeli security vendors into Nigeria. Grim & Scahill highlight a 2014 email where Epstein asks Barak, "With civil unrest exploding in ukraine syria, somolia, libya, and the desperation of those in power, isn't this perfect for you." Barak's reply—"You're right [in] a way. But not simple to transform it into a cash flow"—captures the cynical calculus at the heart of the deal. The authors argue that the "desperation of those in power" was not a tragedy to be solved, but a market condition to be exploited.
This framing is effective because it strips away the humanitarian veneer of "counter-terrorism." The authors show that the initial entry point was a Christian university, Babcock University, which was pitched a power plant but instead purchased biometric surveillance equipment. As Grim & Scahill note, "The pilot helped build relationships between Israeli operators and the Nigerian national security officials, while their partnership was framed as a matter of countering Islamic terrorism." This sectarian subtext allowed foreign actors to embed deep surveillance capabilities under the guise of protecting a minority group, a tactic that echoes the earlier deployment of the "Basel" system at the Erez Crossing in Gaza.
Security cooperation offered an appealing way for Barak and Epstein to generate cash from chaos in Nigeria, while also promoting the political interests of the Israeli government.
Critics might argue that the Nigerian government was an active, willing participant in these deals, seeking any advantage against a brutal insurgency. While true, the authors' evidence suggests the terms were heavily skewed by the leverage of foreign intelligence and capital, turning a sovereign security need into a dependency on opaque, foreign-owned technology.
From Checkpoints to Ports
The narrative deepens as the authors connect these security deals to the broader economic ambitions of the United Arab Emirates and the logistics giant DP World. The piece reveals that Epstein facilitated talks between DP World's former chairman and Nigeria's sovereign investment fund, aiming to secure port ownership in Lagos and Badagry. The authors point out a crucial detail: "DP World's leadership was reluctant to invest in an industrial zone in Nigeria unless they could own the surrounding port outright." This demand for total control highlights the extractive nature of the proposed infrastructure, which would have bypassed local regulatory frameworks.
The coverage draws a direct line between the biometric scanners tested on Nigerian students and the potential for controlling the movement of goods and people at scale. Grim & Scahill explain that Israeli intelligence firms marketed their security know-how as "field-proven," a euphemism for technologies deployed against Palestinians living under Israeli military occupation. The authors write, "Israel's automated checkpoints, equipped with facial and hand-geometry scanners, were touted as a way for African governments to control movement of populations at scale." This parallel is not incidental; it is the core of the business model.
The article also touches on the complex web of sanctions evasion involving mining magnates. Epstein is shown helping navigate around U.S. sanctions on Ivan Glasenberg of Glencore and Oleg Deripaska of Rusal. Grim & Scahill note that "Barak's hacked emails... show Barak parlaying his Nigeria security relationships into oil investment opportunities, with Epstein's steady guidance." This connection to Glencore is particularly significant given the firm's history of corruption scandals in the Democratic Republic of Congo, suggesting a pattern of using security deals to bypass legal and ethical constraints in resource-rich regions.
The authors do not shy away from the human cost of this expansion. They recount how the "in-motion identification" system at Babcock University allowed for the authentication of students from a distance, with a press release boasting that the technology would "help guarantee safety on campus by filtering away all unwanted persons." The phrase "unwanted persons" carries a heavy weight, evoking the dehumanizing logic of the very checkpoints the technology was designed for.
"Palestinians were standing in the [queue] to enter Israel for four, five, or even six hours," a spokesperson explained. "The military was trying to make sure that no one passing through the checkpoint was a terrorist or on a watch list."
The authors use this quote to illustrate the "convenience" argument used to sell surveillance to the public, a narrative that was then exported to Africa. The irony is palpable: technology designed to manage the humiliation of occupation was sold to a Nigerian university as a safety feature.
The Long Game
The piece concludes by showing how these initial pilots evolved into institutional partnerships. By 2020, the World Bank had tapped the Israel National Cyber Directorate to shape Nigeria's cyber infrastructure, a move that solidified the influence of these foreign actors. Grim & Scahill write, "This playbook illustrates a clear through-line for Epstein and Barak's Africa strategy: Counter-terrorism partnerships opened doors and foreign investors seeking energy and mining deals walked through them."
The authors also reveal the extent of Epstein's personal involvement in these networks, noting his connections to Silicon Valley figures like Peter Thiel and his role in funding startups like Reporty Homeland Security. The article details how Epstein loaned Barak $1 million to invest in security ventures, cementing a financial bond that went beyond mere consulting. "We miss you. Never a dull moment here," Barak emailed Epstein after a major investment, signaling the personal and professional entanglement of these men.
The coverage ends with a look at the future implications of these deals. As of July 2025, an Israeli firm had installed cyber warfare simulators at Babcock University to train the next generation of cybersecurity operators. This suggests a long-term strategy to embed Israeli doctrine and technology into the very fabric of Nigeria's security apparatus.
Critics might note that the article relies heavily on leaked emails, which, while corroborated by other sources, can sometimes be taken out of context. However, the sheer volume of correspondence and the specific details regarding dates, names, and financial transactions lend significant credibility to the authors' reconstruction of events.
"This is going to be fun," Epstein wrote in a 2010 email about a potential oil deal, revealing a casual, almost gleeful attitude toward the high-stakes manipulation of African resources.
Bottom Line
Ryan Grim & Jeremy Scahill have produced a devastating exposé that reframes the narrative of African security cooperation, revealing it as a vehicle for surveillance export and resource extraction. The strongest part of their argument is the unflinching connection between the biometric technologies used in Gaza and those deployed in Nigeria, proving that the "security industrial complex" treats human rights as a secondary concern to profit. The biggest vulnerability of this story is its complexity; the web of actors is so dense that it risks overwhelming the reader, though the authors manage this by focusing on the clear through-line of technology and money. Readers should watch for the ongoing implementation of these biometric systems in Nigeria, as they represent a permanent shift in how African populations are monitored and controlled.