In an era where digital footprints are harvested as casually as rainfall, a new guide cuts through the noise to argue that true anonymity isn't about hiding in the shadows, but about blending into the crowd. The Hated One presents a stark reality: the internet is a network of other people's computers, and without specific intervention, your location and identity are broadcast to every server you touch. This isn't just a technical manual; it is a manifesto on the necessity of operational security for anyone who values privacy in a surveillance economy.
The Architecture of Anonymity
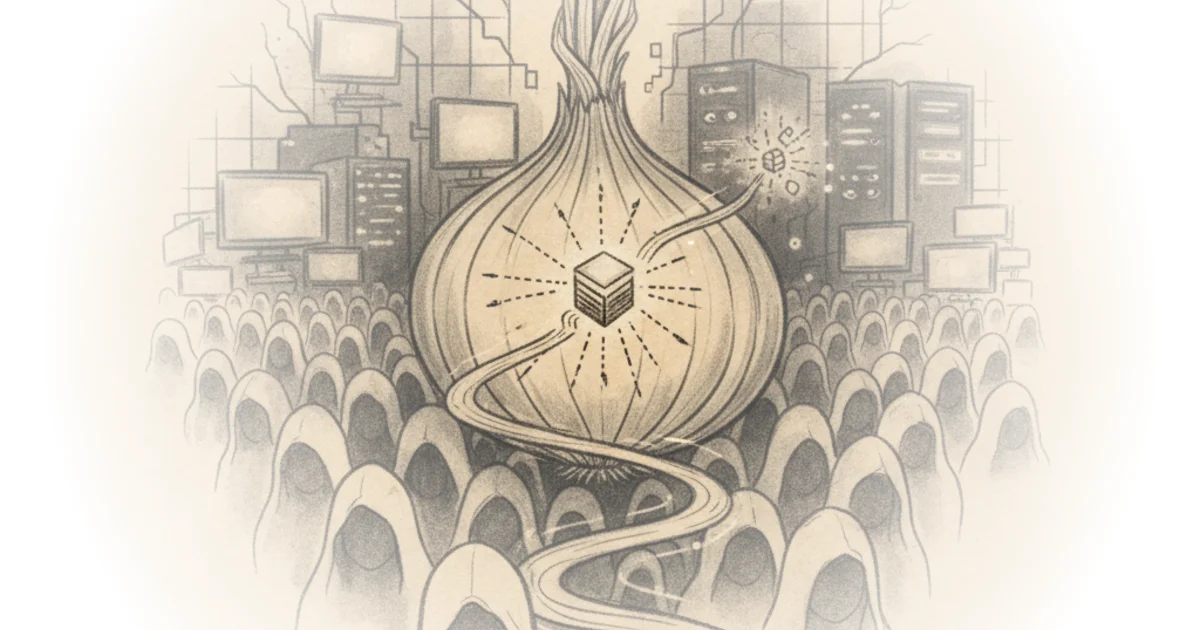
The core of the argument rests on a powerful metaphor. The Hated One writes, "Tor is designed to give all of its users the same identity; it's as if a crowd of people in the streets all wear the same clothes and the same mask." This framing effectively demystifies the complex routing protocols of The Onion Router, reducing them to a simple concept of collective camouflage. The author explains that while standard browsing reveals your true location to thousands of computers daily, Tor hides this by relaying traffic through three random global locations with triple-layer encryption.
This approach is compelling because it shifts the focus from "hiding" to "obscuring." The Hated One notes that Tor is "essentially a traffic analysis resistance tool" that doesn't stop data collection but ensures the collected data "can't be meaningfully deciphered and utilized." This is a crucial distinction often missed in mainstream privacy discussions. However, critics might argue that this reliance on network-level obfuscation ignores the growing sophistication of traffic correlation attacks by well-funded state actors, which can sometimes de-anonymize users even without breaking encryption.
"Tor is just a tool; it can only do as much as the piece of monkey meat that's using it."
The Human Element of Security
The guide's most valuable contribution lies in its shift from software configuration to behavioral discipline. The Hated One argues that technology alone is insufficient without rigorous "operation security," or OPSEC. The author lists non-negotiable rules, such as never using real identities for accounts and avoiding the mixing of anonymous and non-anonymous activities. As The Hated One puts it, "If you create a fake pseudonym on Tor and then use or even mention that pseudonym anywhere outside of Tor, you are compromised."
This section highlights a critical vulnerability in modern digital life: the human tendency to compartmentalize poorly. The author warns that advanced trackers can link a Tor session to a real identity if a user runs scripts from the same provider on both the clear web and the Tor network. For instance, watching a video on a standard app and then searching for the same topic on Tor can create a digital bridge that exposes the user. The Hated One emphasizes that "if you make a connection to the same provider anonymously and non-anonymously at the same time, you're screwed." This blunt assessment serves as a necessary reality check for users who believe a browser extension is a magic shield.
Hardening the Browser
Moving to practical application, the commentary details specific configurations required to maximize safety. The Hated One advises against the default settings, which prioritize user-friendliness over security. "The only way you should do this is to change the security level to safer or the safest mode," the author insists, explaining that the safest mode disables all JavaScript and media by default. This is a significant departure from how most people use the web, where scripts run automatically.
The guide also recommends blocking all unencrypted connections via the HTTPS Everywhere extension, noting that in the current landscape, "I don't want to visit any website that isn't encrypted." The Hated One further advises against installing unofficial plugins or changing settings in ways that make a user's browser fingerprint unique. The logic is sound: "Making any other changes to the browser... is like putting a giant stick on the forehead of your anonymous mask; it makes you stand out from the crowd."
Critics might note that the "safest" mode renders much of the modern web unusable, creating a high barrier to entry that could discourage average users from adopting these tools at all. Yet, the author's stance remains firm: if you want anonymity, you must accept the friction it creates.
Bottom Line
The strongest part of this piece is its unflinching focus on user behavior over technical hacks, correctly identifying that the weakest link in any security chain is the person behind the keyboard. Its biggest vulnerability is the assumption that users can consistently maintain the high level of discipline required to avoid cross-contamination between their anonymous and real-world digital lives. For the busy professional, the takeaway is clear: privacy is not a setting you toggle once, but a continuous practice of restraint and verification.