Chris Chappell delivers a chilling exposé on the mechanics of state-sponsored information warfare, moving beyond the familiar trope of simple internet censorship to reveal a sophisticated, paid ecosystem designed to manufacture public opinion. The piece's most arresting claim is that the Chinese Communist Party didn't just delete dissent during the pandemic; they actively flooded the digital space with subtle, state-paid narratives to shape global perception, a strategy that relied on Western technology and a vast bureaucracy of human actors. For busy readers tracking the origins of the pandemic and the integrity of global health data, this breakdown of the "online public opinion management" apparatus offers a critical lens on why the truth has been so hard to pin down.
The Architecture of Narrative Control
Chappell argues that the revelation of 32,000 directives and 1,800 memos, obtained by anti-CCP hackers and reported by the New York Times, exposes a system far more complex than a simple firewall. He writes, "It's not just about censorship... they're very much trying to shape what people talk about." This distinction is vital; it shifts the focus from what is missing to what is being artificially constructed. The author details how, following the death of whistleblower Dr. Li Wenliang, the state issued specific orders to suppress his name from trending and to flood platforms with alternative topics. The strategy was not brute force but subtlety. As Chappell notes, the directives instructed operators that "when you're guiding public opinion you can't just be sarcastic or patriotic you need to be sleek and silent in achieving results."
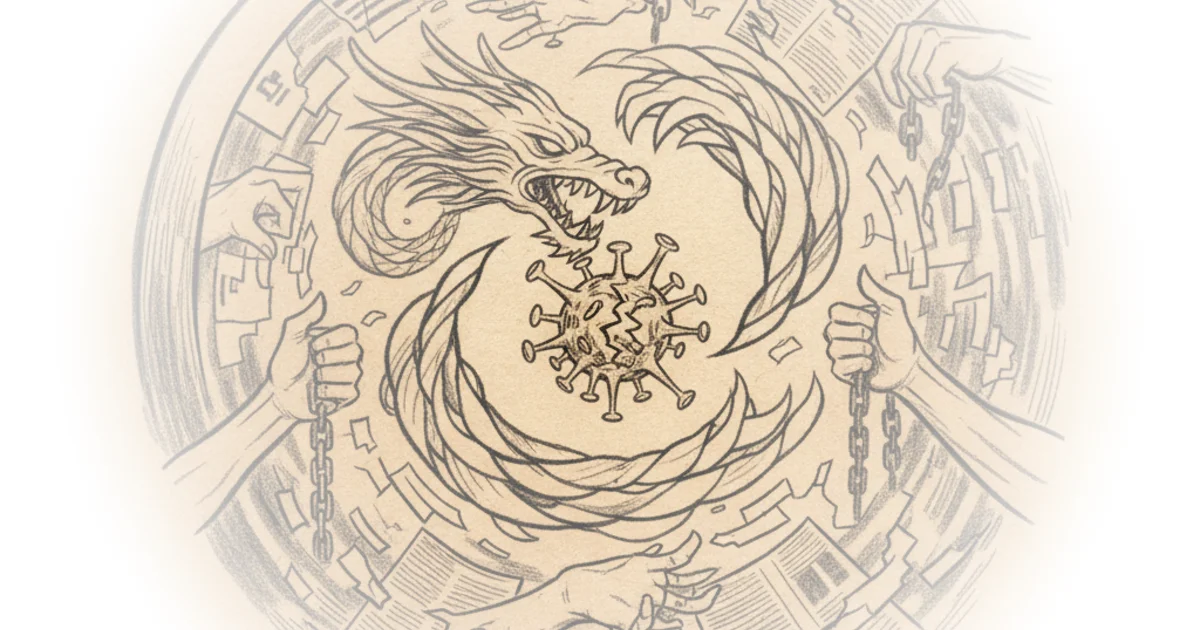
This framing is effective because it demystifies the "invisible hand" of state propaganda. It wasn't just a top-down order to silence; it was a coordinated effort to drown out truth with a sea of manufactured consensus. The evidence suggests a massive infrastructure was built to execute this, involving private contractors and specialized technology. Chappell points out the irony that "it takes an enormous bureaucracy armies of people specialized technology made by private contractors... who probably got their technology from the west." The reliance on Western tools to suppress Western-style free speech creates a paradoxical vulnerability in the global information ecosystem.
"They have this whole um basically they have technology that lets them do things like they would let you know these paid internet commenters that work for you know the state... to for example mass-like posts so you didn't have to go through and like like each individual you know fake post posted by these internet commenters but you could just boost them artificially."
The financial incentives driving this machine are stark. Chappell highlights specific payment structures found in the leaked documents, noting that in Guangzhou, "you could be paid 25 for an original post longer than 400 characters if you flag a flagging a negative comment for deletion earns you 50 cents and reposts are worth one cent a piece." This gamification of disinformation turns ordinary citizens into unwitting agents of state policy. Critics might argue that the scale of such operations is often exaggerated by political opponents, but the specificity of the leaked memos regarding payment rates and content guidelines lends significant credibility to the claim that this is a formalized industry.
The Global Reach and the Origin Cover-Up
The commentary expands to show how these domestic tactics were projected outward to manage international opinion. Chappell explains that the administration was deeply concerned about reports of China buying up global supplies of personal protective equipment, fearing it would look like hoarding. Consequently, they were told "don't use the word fatal don't say that you know this is incurable call them lockdowns when they started you know locking down different areas of the country." This linguistic sanitization was a deliberate attempt to downplay the severity of the crisis.
More disturbingly, the piece connects this narrative management to the obstruction of the virus's origin investigation. Chappell describes how reporters from the BBC were physically prevented from investigating a mine in Yunnan province, a site linked to the Wuhan Institute of Virology, where samples of a similar coronavirus were taken years prior. The author notes that "all of their online data had been taken down and when asked the lab was oh well we were hacked so we took all our our data down to uh you know for safety." This pattern of obstruction—blocking physical access, deleting digital records, and blaming technical failures—suggests a coordinated effort to prevent independent verification. Chappell observes that "the way the chinese countries party keeps trying to blame like the u.s or india or italy for being the start of the coronavirus just the way they have made it impossible to investigate the origin of the coronavirus."
The argument here is that the cover-up was not a passive reaction but an active strategy. By controlling the narrative domestically and internationally, the executive branch in Beijing successfully delayed the global response and obscured the facts. The author suggests that the World Health Organization's subsequent decision to look in caves in Southeast Asia rather than the specific site in China is a direct result of this successful pressure. "Well don't worry the world health organization has agreed not to investigate the origin of the coronal virus so actually you know what they're going to do they're going to go to southeast asia and look in caves for bat coronaviruses," Chappell remarks with biting irony. This highlights the ultimate success of the propaganda machine: redirecting the world's attention away from the most suspicious locations.
The Zoom Precedent: Data as a Weapon
The piece pivots to a second, equally alarming development involving Zoom and the arrest of a Chinese executive, Julian Jin. Chappell details how Jin acted as a liaison between the video conferencing company and Chinese intelligence agencies, providing user data and facilitating the shutdown of meetings commemorating the Tiananmen Square massacre. The author writes, "he was directly working with the chinese communist party's police like the public security bureau and the ministry of state security the intelligence service and he was looking at u.s user data and sending that to uh china's intelligence services and police."
This section underscores the danger of global tech platforms operating under the jurisdiction of authoritarian regimes. Jin didn't just hand over data; he actively fabricated evidence to justify censorship. Chappell explains that "he did it by like fabricating uh uh information that these people were involved in terrorism or racist violence or even child pornography" to get Zoom's US executives to ban dissidents. The implication is that the platform's compliance with local laws was a cover for active participation in human rights abuses. The author notes that the Chinese government used this intelligence to "detain dissidents in china and to also harass the family members of dissidents who were in the us."
"It is incredibly uh explosive and concerning that you know all the things that we thought about zoom were actually happening and i do have to say that the chinese communist party directly used this information to detain dissidents in china and to also harass the family members of dissidents who were in the us."
The argument here is that the threat is not theoretical; it is operational and has already caused real-world harm. While Zoom has defended its actions by citing compliance with local laws, Chappell's analysis suggests that this defense is insufficient when the "local law" is used as a tool for political persecution. The arrest warrant and the Department of Justice's involvement signal a shift in how US authorities are treating these data breaches, moving from corporate negligence to criminal conspiracy. Critics might argue that the US government is overreacting to a standard business practice, but the specific targeting of political dissidents and the fabrication of criminal charges make this case distinct from typical data privacy disputes.
Bottom Line
Chris Chappell's commentary succeeds in connecting the dots between domestic censorship, global narrative manipulation, and the weaponization of tech platforms, presenting a cohesive picture of how the Chinese Communist Party operates in the information age. The strongest part of the argument is the detailed evidence of paid narrative shaping, which moves the discussion from abstract censorship to a tangible, industrial-scale operation. However, the piece's reliance on leaked documents and the inherent difficulty of verifying the full scope of the WHO's internal decision-making leaves some room for skepticism regarding the total extent of the cover-up. Readers should watch for the outcome of the DOJ case against Julian Jin, as it may set a critical precedent for how American tech companies are held accountable for collaborating with foreign intelligence services.
"It takes an enormous bureaucracy armies of people specialized technology made by private contractors... who probably got their technology from the west the constant monitoring of digital news outlets and social media platforms and presumably lots of money."
The ultimate takeaway is that the battle for the truth is not just about facts, but about the infrastructure used to disseminate them. As long as the tools of communication are vulnerable to state capture, the narrative will remain a contested battlefield.