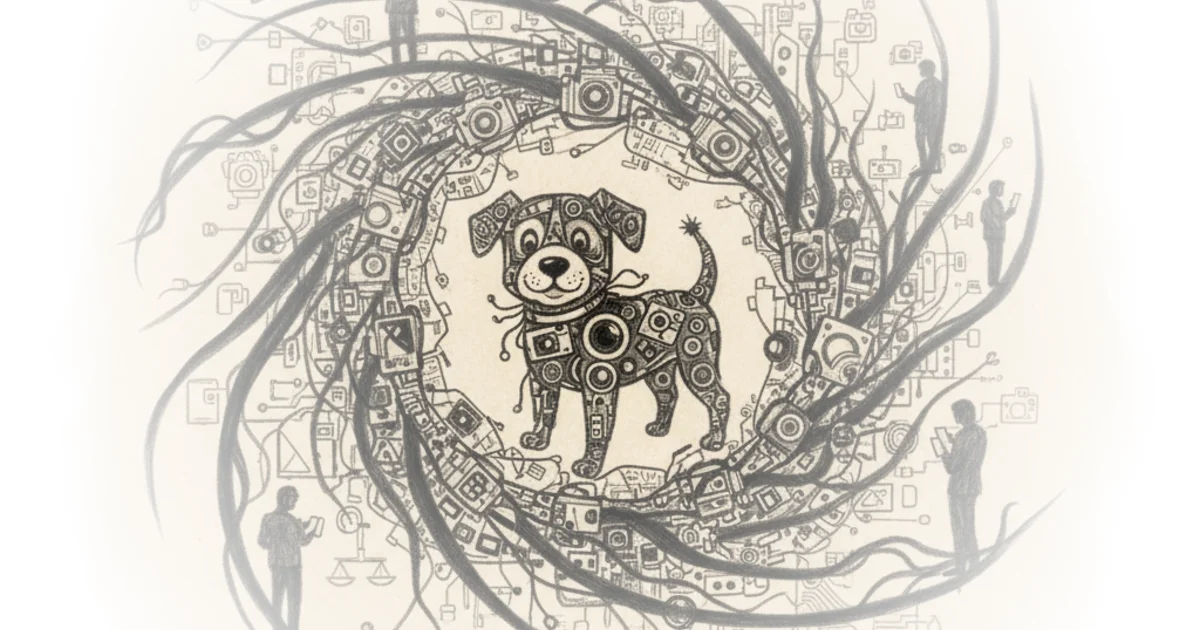
Devin Stone cuts through the Super Bowl spectacle to expose a chilling reality: a commercial about finding lost dogs was actually a test run for a crowdsourced surveillance state. He argues that the proposed partnership between Ring and Flock Safety wasn't just a corporate merger, but a potential constitutional breach that slipped past public scrutiny until the ad aired. This is not merely about privacy; it is about the legal mechanisms that allow private technology to bypass the Fourth Amendment's warrant requirement.
The Illusion of Consent
Stone begins by dissecting the Ring Super Bowl ad, noting how it normalized the idea of neighbors scanning each other's footage through AI. He writes, "They saw a crowdsourced surveillance state." This framing is crucial because it shifts the narrative from individual safety to collective monitoring. The author points out that while Ring and Flock claimed their partnership was separate from the "Search Party" feature, the timing was suspicious, coinciding with heightened immigration enforcement and local debates over police cooperation with federal agencies.
The core of Stone's argument rests on the distinction between voluntary sharing and automated data harvesting. He explains that Ring's current model relies on neighbors voluntarily handing over footage after a crime, a process where consent is the primary legal shield. "Once a member of the public hands over authorization to access their camera, the footage becomes evidence and the person surrenders their right to do a takes back," Stone observes. This is a sharp legal insight: the system is designed to function on the back end of consent, creating a pipeline where private data becomes public evidence without a warrant.
Critics might argue that voluntary cooperation is a cornerstone of community policing and that Stone is overstating the coercion involved. However, the author effectively highlights the strategic corporate maneuvering behind this. By routing data through Axon, the same company managing police body cameras, Ring and Flock achieve a "strategic corporate move" that allows them to provide forensic evidence to law enforcement while maintaining plausible deniability with the public.
The Loophole of Indirect Access
The commentary takes a darker turn when addressing how federal agencies access this data. Stone notes that even if Ring claims no direct partnership with Immigration and Customs Enforcement (ICE), the architecture of the system creates a massive loophole. "That's a pretty big loophole because it means that even if Flock doesn't give ICE direct access, the system can still be used that way in practice," he writes. This is the piece's most alarming claim: federal authorities can bypass direct restrictions by asking local police to run searches on their behalf.
He supports this with a report of a Texas police department conducting a warrantless nationwide search of over 83,000 cameras for a specific reason logged as "had an abortion, search for female." While the partnership was canceled following public backlash, Stone asks the pivotal question: "Could they have gotten away with it legally if the internet outrage machine hadn't given them cold feet?" This suggests that the legal framework is currently insufficient to stop such overreach, relying instead on public relations pressure.
The Mosaic Theory and the Fourth Amendment
Stone then pivots to the legal battleground, contrasting two judicial approaches to automated license plate readers (ALPRs). He references the Supreme Court's 2017 decision in Carpenter v. United States, which established that long-term cell phone location tracking constitutes a search requiring a warrant. Stone connects this to the Norfolk, Virginia case, where a court ruled that Flock's scattered snapshots did not violate the Fourth Amendment because they didn't create a continuous timeline.
However, the author highlights a more nuanced view from Massachusetts in Commonwealth v. McCarthy. Here, the court engaged with the "mosaic theory," acknowledging that while a single data point is public, the accumulation of many points reveals a detailed picture of a person's life. Stone writes, "While we cannot say precisely how detailed a picture of the defendants's movements must be revealed to invoke constitutional protections, it is not that produced by four cameras at fixed locations on the ends of two bridges." This distinction is vital: the law is struggling to define the threshold where ordinary policing becomes unconstitutional surveillance.
"It doesn't matter if your government stalker is wearing a blindfold the whole time they're tracking you, waiting for you to do some crime. Still an unreasonable search."
This quote captures the essence of the Fourth Amendment debate: the intent of the tracker is irrelevant if the result is a comprehensive invasion of privacy. Stone notes that in the Baltimore aerial surveillance case, Leaders of a Beautiful Struggle v. Baltimore Police Department, courts struck down the program because it allowed police to "reconstruct people's lives retroactively." He draws a historical parallel to the "Gorgon Stare" technology used in the global war on terror, reminding readers that this level of surveillance is not new, but its application to domestic civilian life is the real danger.
The Unresolved Tension
The piece concludes by looking at the active litigation in San Jose, where the Electronic Frontier Foundation is challenging the city's use of Flock cameras. Stone points out that while San Jose police scan hundreds of millions of cars, the legal system has yet to definitively rule on whether this mass data collection violates the Constitution. He notes that the Norfolk court distinguished Flock from the Baltimore program by claiming it didn't build full travel histories, but Stone warns that constitutional rulings are based on current practices, not future possibilities.
A counterargument worth considering is that the technology itself is neutral and that the legal framework is simply lagging behind innovation. Stone acknowledges this by noting that courts are hesitant to rule on what a system "might" do in the future. However, his analysis suggests that waiting for a catastrophic misuse of data before establishing constitutional boundaries is a dangerous strategy. The reliance on the "mosaic theory" in Massachusetts offers a glimmer of hope, but as Stone notes, the specific record in that case was too narrow to trigger full Fourth Amendment protections.
Bottom Line
Devin Stone's commentary is a potent reminder that the most significant threats to privacy often arrive disguised as community safety tools. His strongest argument is the exposure of the "indirect access" loophole, which allows federal agencies to bypass warrant requirements through local intermediaries. The piece's biggest vulnerability is its reliance on the assumption that public outrage will consistently serve as the only effective check on corporate and government overreach, a strategy that is neither reliable nor democratic. Readers should watch the San Jose litigation closely, as it may finally force the courts to define the constitutional limits of the mosaic theory in the age of automated surveillance.