Ross Haleliuk cuts through the noise of the cybersecurity industry with a simple, devastating truth: there is no single definition of security because there is no single way to build a security program. He argues that the field's chronic disagreements stem not from incompetence, but from the diverse, non-standardized backgrounds of the people leading it. For busy leaders trying to navigate a fragmented landscape, this reframing turns confusion into a strategic asset.
The Architecture of Perspective
Haleliuk begins by dismantling the myth of a shared professional foundation. Unlike accounting or biology, where formal education creates a common baseline, security professionals arrive from "all walks of life," learning on the job. He writes, "There isn't much of a shared baseline. People come in from all walks of life, learn on the job, and only later pick up more standardized knowledge through certifications or experience." This observation is crucial because it explains why a CISO from a software background might view a vulnerability as a code flaw to be patched, while one from a compliance background sees it as a regulatory liability to be documented.
The author's analysis of how specific backgrounds shape mental models is particularly sharp. He notes that leaders with software engineering roots "tend to see security as something you can build and improve through better systems," often treating it as a competitive advantage. In contrast, those with IT infrastructure backgrounds focus on the gritty reality of "keeping the business running" across thousands of employees, prioritizing visibility and reliability over architectural elegance. This distinction matters deeply for organizations trying to implement new tools; a solution that delights an engineering team might fail to address the operational constraints of a massive, legacy-heavy enterprise.
"Each person in security comes with a completely different mental model. So who's right? They are all right, and they are all wrong at the same time."
This insight echoes the historical challenges of "Security through obscurity," a concept Haleliuk's publication has explored in depth. Just as relying on secrecy failed because it assumed attackers would never see the inner workings of a system, relying on a single security perspective fails because it assumes one view can capture the entire threat landscape. Haleliuk suggests that the industry's diversity is a feature, not a bug, but only if leaders can synthesize these disparate views.
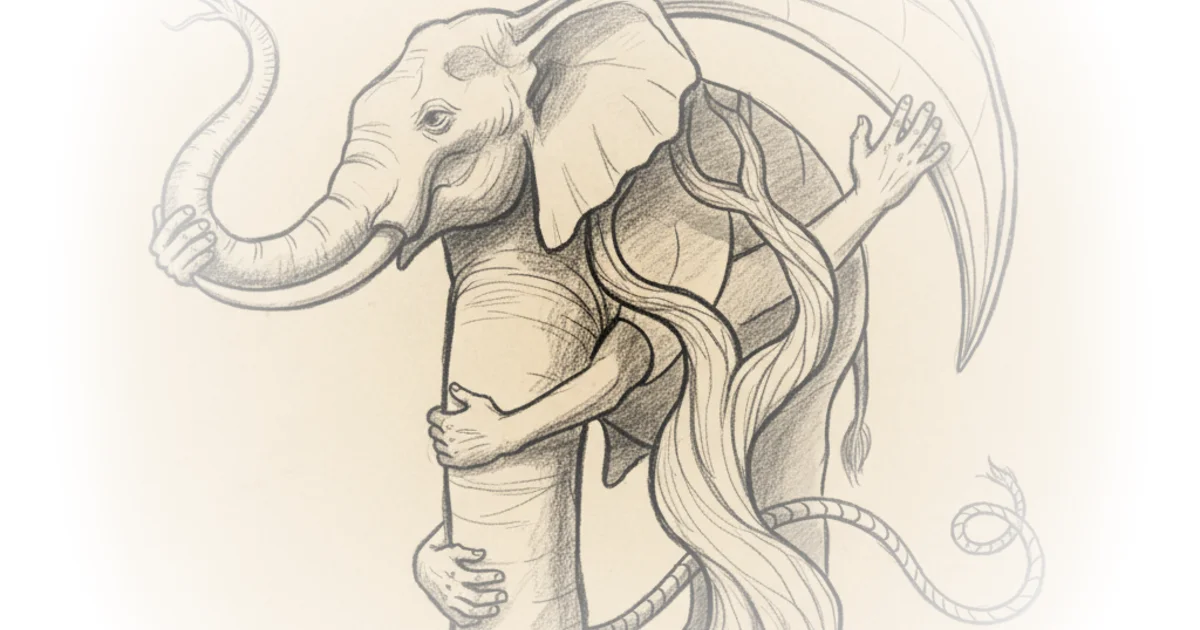
The Elephant in the Room
The second dimension of Haleliuk's argument shifts from the people to the environment. He argues that "there's no single right way to secure a company, because there's no single definition of what needs to be secured." A B2B software platform faces fundamentally different risks than a hospital or a manufacturing plant. The author warns that the industry often forgets this reality, leading to generic advice that fails in specific contexts.
He illustrates this by contrasting the needs of different sectors. A former law enforcement professional might excel at "investigation and accountability," building strong incident response teams, while a leader with a military background focuses on "defense strategy, planning, and execution," ensuring disciplined preparation for worst-case scenarios. Neither approach is universally superior; their value depends entirely on the organization's specific constraints and threat model. Haleliuk points out that panels featuring only SaaS CISOs offer limited value compared to diverse groups representing regulated industries, operational technology, and other sectors.
Critics might argue that this relativism makes it harder to establish industry-wide standards or baseline security postures. If every organization is an "elephant" of a different shape, how do regulators or auditors enforce consistency? However, Haleliuk's point is not that standards don't exist, but that their application must be nuanced. As he puts it, "It's all these nuances that make specific controls very effective or utterly useless."
"Real security comes from understanding the system, the business, the risks, and the tradeoffs as a whole, and figuring out what is appropriate for this specific environment at this specific stage."
This perspective challenges the "one-size-fits-all" mindset that often plagues procurement and policy. It suggests that the most effective security leaders are those who can translate their specific background into a broader understanding of the organization's unique risks, rather than forcing their organization to fit a pre-existing mold.
Bottom Line
Haleliuk's strongest contribution is the reframing of security disagreements as a natural result of diverse expertise rather than a failure of leadership. His argument holds up well against the reality of modern, complex enterprise environments where a single technical fix rarely solves a systemic risk. The biggest vulnerability in this approach is the difficulty of execution: synthesizing these conflicting perspectives requires a level of cross-functional fluency that many organizations struggle to achieve. Leaders should watch for how their own teams' backgrounds are shaping their risk appetite and ensure they are not inadvertently building security programs that only solve for one part of the elephant.