Most consumers assume their smartphone is a fortress, but this piece argues the opposite: it is a meticulously designed data mine disguised as a sanctuary. The Hated One dismantles the prevailing narrative that Apple is a privacy champion, revealing instead a corporation that monetizes user behavior through legal loopholes and opaque definitions. For anyone relying on a single device for their digital life, this analysis exposes a critical vulnerability that goes far beyond simple advertising.
The Myth of the Privacy Alternative
The core of the argument rests on a fundamental rejection of trust in centralized ecosystems. The Hated One writes, "there is no cloud only other people's computers," a blunt reminder that data stored on Apple's servers is subject to their control, not the user's. The author contends that Apple's marketing strategy relies on a "disingenuous trend among the big tech companies where they can deceive the public seeking more information about their practices." This framing is effective because it shifts the blame from technical complexity to intentional obfuscation.
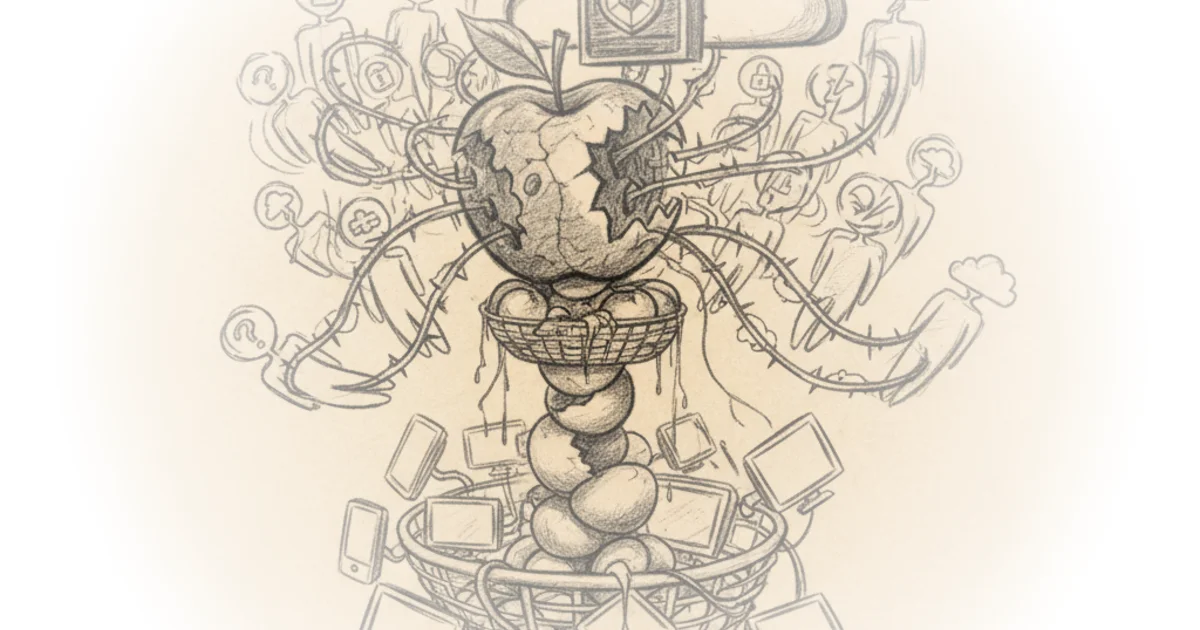
The piece meticulously details how Apple collects an exhaustive range of data, from location and browsing history to reading habits and messaging metadata. The Hated One asserts, "apple collects every piece of data they are capable of collecting... and that's just scratching the surface." This evidence challenges the common perception that Apple's business model is purely hardware-driven. Instead, the author argues that "their business model is not about protecting your data it's about increasing the shareholder value." This is a crucial distinction for investors and consumers alike, suggesting that privacy is merely a feature to be sold, not a right to be upheld.
Critics might note that Apple's hardware integration does offer genuine security benefits against external hackers that fragmented Android ecosystems sometimes lack. However, the author counters that this security is illusory if the platform itself is the primary data collector.
The Loophole of "Non-Personal" Data
Perhaps the most technical and damning section of the commentary focuses on how Apple redefines what constitutes personal information. The Hated One explains that Apple's advertising identifier is classified as "non-personal," yet it is the very tool third-party developers use to track users across the web. The author writes, "you would consider an os level identifier that can track your activity with ads to be pretty personal." This disconnect between legal definitions and user expectations is where the real danger lies.
The piece highlights a specific loophole regarding location data. Even when developers are instructed to de-identify location information, the author notes, "it's impossible to de-identify your location info your location is your identity." By combining this with the fact that Apple reserves the right to enrich its own databases with data collected from third parties, the argument becomes clear: the safeguards are porous. The Hated One points out that "apple combines their non-personal data collected by cookies pixel tags and other technologies with personal data they already hold," effectively bypassing the very restrictions they place on others.
Your location is your identity. The pattern of places you approximate at a given time is unique.
The Illusion of Control and Encryption
The commentary also scrutinizes the user interface features designed to give an illusion of control, such as the opt-out settings for advertising. The Hated One argues that "this isn't a feature that protects user privacy and it certainly doesn't give them more choice it's apple's move to monopolize their market share." The author notes that while users can opt out of third-party ad tracking, Apple's own advertising network uses the Apple ID, an identifier that third parties are forbidden from using. This creates a preferential system where Apple retains superior tracking capabilities.
Furthermore, the piece addresses the encryption debate, specifically regarding iCloud backups. The Hated One writes, "some of this is not encrypted such as apple car transactions health data and icloud keychain with your saved accounts and passwords." The author suggests that Apple's decision to drop plans for end-to-end encryption for all data was a direct result of pressure from the FBI, noting that "the fbi complained it would deny them access to user data so apple just decided to drop it." This contradicts the public image of Apple as a defender of civil liberties against government overreach.
A counterargument worth considering is that full encryption would indeed prevent law enforcement from accessing data in legitimate criminal investigations, a balance that is difficult to strike. Yet, the author maintains that Apple's compliance rate—fulfilling 82 percent of US government data requests in 2020—reveals a company that prioritizes cooperation over absolute user privacy.
The Bottom Line
The strongest part of this argument is its exposure of the semantic games played by tech giants to classify invasive tracking as benign data analysis. The piece's biggest vulnerability is its absolute dismissal of any security benefit Apple provides, which may alienate users who prioritize device security over data sovereignty. The reader should watch for how regulatory bodies begin to address the definition of "personal data," as that will determine whether Apple's current practices remain legal or become the next major privacy scandal.
Your privacy is not a fundamental human right; it's an asset that can be analyzed to study your behavior and personalize your response to it.