Tim Mak's reporting cuts through the noise of battlefield statistics to reveal a quieter, more insidious front in the war: the weaponization of human trust. While the world watches tank movements, the author exposes how Russian hybrid warfare has evolved from massive server crashes to intimate, psychological manipulation of ordinary citizens. This piece is notable because it treats cyberfraud not as a nuisance, but as a deliberate tactic to erode morale and drain resources from a society already under siege.
The Evolution of Hybrid Warfare
Mak anchors his argument in the personal story of Valentyna Dzuba, a retired woman in Dnipro whose routine was shattered by a single click. The author writes, "During wartime, internet scams have become part of broader Russian hybrid attacks aimed at destabilizing society from within, especially when it is already under constant tension." This framing is crucial; it shifts the narrative from individual gullibility to systemic targeting. The piece effectively illustrates how the enemy exploits the very fabric of community—friendships, family bonds, and charitable instincts—to inflict damage.
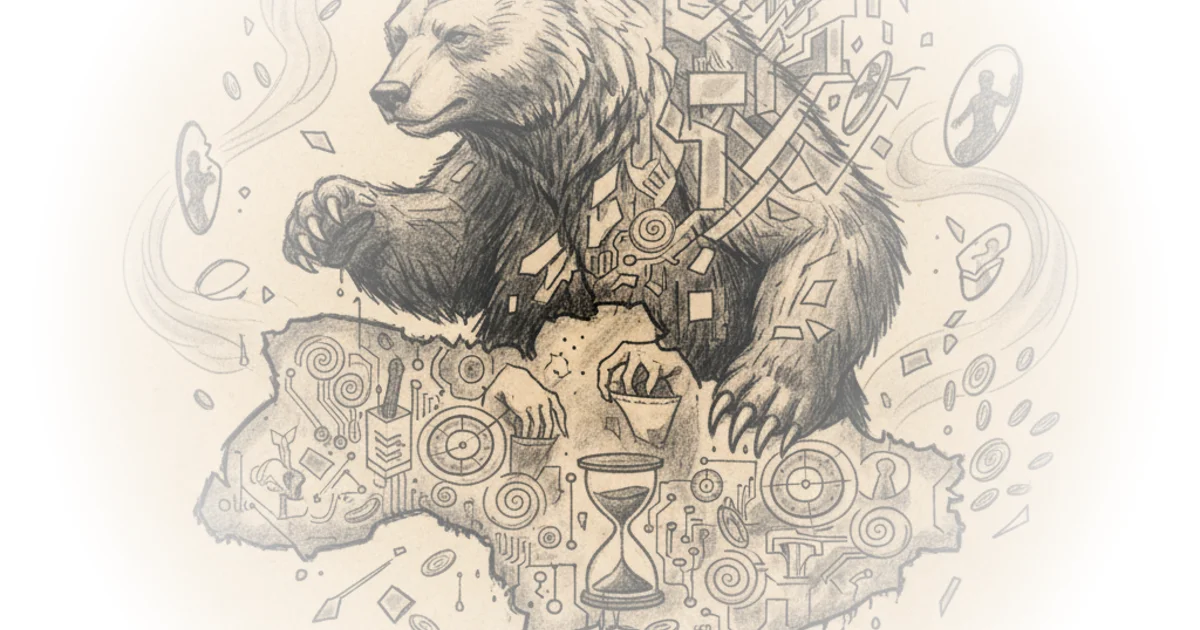
The author draws a direct line from the early days of the conflict to the present, noting that "Russia began its hybrid attacks in cyberspace against Ukraine long before its full-scale invasion, extending warfare beyond land." Mak provides historical depth by referencing the eight-minute DDoS attack in March 2014, which crippled government websites just days before the Crimea referendum. This context is vital for understanding the sophistication of the current threat. It wasn't an accident; it was a playbook. The evolution from those large-scale, clumsy attempts to delete election files in 2014 to today's surgical strikes on individual Telegram accounts shows a terrifying adaptation by the adversary.
"Scammers don't pick phone numbers at random. They buy your data from brokers."
This observation, while seemingly obvious in the West, carries a different weight in the context of a nation under invasion. The author connects this to the broader ecosystem of data theft, a theme that resonates with the deep dive on data brokers. Just as the 'Fancy Bear' group targeted EU personal accounts in January to steal data, the current operations in Ukraine use similar infrastructure to harvest identities. The damage is identical: stolen personal data, hacked accounts, and financial ruin. The author's ability to weave these disparate threads—historical cyberattacks, modern data brokerage, and personal tragedy—into a cohesive narrative is the piece's greatest strength.
The Mechanics of Deception
The article excels in explaining the technical and psychological mechanisms behind the scams without getting bogged down in jargon. Mak introduces Lieutenant Colonel Oleksandr Ulianenkov, who explains that scammers rely on "social engineering," a manipulation tactic that bypasses security by exploiting human emotion. The author writes, "Scammers call or message potential victims using scripts designed to create emotional pressure: sick children, urgent medical treatment, missing soldiers, or energy shortages."
This is where the commentary becomes most urgent. The author argues that these attacks work because they target the brain's automatic responses. "People often don't realize they're being scammed because scammers exploit how our brains work," Mak notes. "They play on emotions like fear, trust, or greed, emotions that cause the average person to trust authority or friends automatically." This analysis holds up under scrutiny; it explains why even the most intelligent people fall victim. The author also highlights the "optimism bias," where victims believe "it won't happen to me," a psychological blind spot that scammers actively hunt.
The piece also tackles the specific role of Telegram, a platform that has become a double-edged sword. Mak points out that "Telegram is a messenger that had previously been flagged in Ukraine as potentially risky as it has a relatively low level of encryption, which makes it easier for scammers and intelligence services to access personal data." The author details how hackers can steal cookie files to bypass passwords entirely, a technical detail that underscores the severity of the threat. A counterargument worth considering is whether blaming the platform's encryption is fair, given its widespread use for legitimate communication and coordination in a war zone. However, Mak balances this by noting that the app has been used to interrogate prisoners and spread disinformation, suggesting the risk is inherent to its architecture in this specific context.
The Human Cost and Resilience
Despite the grim tactics described, the author finds a thread of resilience in Valentyna's story. After realizing her account was compromised, she didn't retreat; she acted. "Cybercriminals have no limits," Ulianenkov warns, yet the response from the community and local technicians offers a glimmer of hope. The author writes, "When Valentyna returned to the workshop the next day, specialists found that one of the scammers was Russian. The technicians laughed. 'You caused quite a panic,' they told her. 'The scammers realized you were not an easy target and disconnected themselves from your contact list.'"
This moment is powerful because it humanizes the conflict. It shows that while the adversary is sophisticated, they are also opportunistic and willing to cut their losses when faced with resistance. The author concludes by noting that Valentyna now "guards her phone the way people double-check their door locks at night," a metaphor that perfectly captures the new reality of daily life in Ukraine. The piece ends on a defiant note: "Let the scammers know there are no fools left."
Critics might argue that focusing on individual vigilance places too much burden on the victim rather than demanding more robust state-level infrastructure. However, Mak's inclusion of the police's new automated systems to freeze funds and block phishing links suggests a dual approach is emerging. The state is building the shield, but the citizen must learn to hold it.
Bottom Line
Tim Mak's coverage is a masterclass in connecting the dots between high-level hybrid warfare and the intimate reality of a grandmother's garden. Its strongest asset is the refusal to treat cyberfraud as a side story, instead positioning it as a central pillar of the Russian strategy to break Ukrainian morale. The piece's vulnerability lies in the sheer scale of the problem; while individual stories like Valentyna's offer hope, the systemic nature of data brokerage and the speed of technological adaptation mean the threat will persist long after this article is read. Readers should watch for how Ukrainian authorities balance the need for open communication with the imperative to secure digital identities in an increasingly hostile environment.