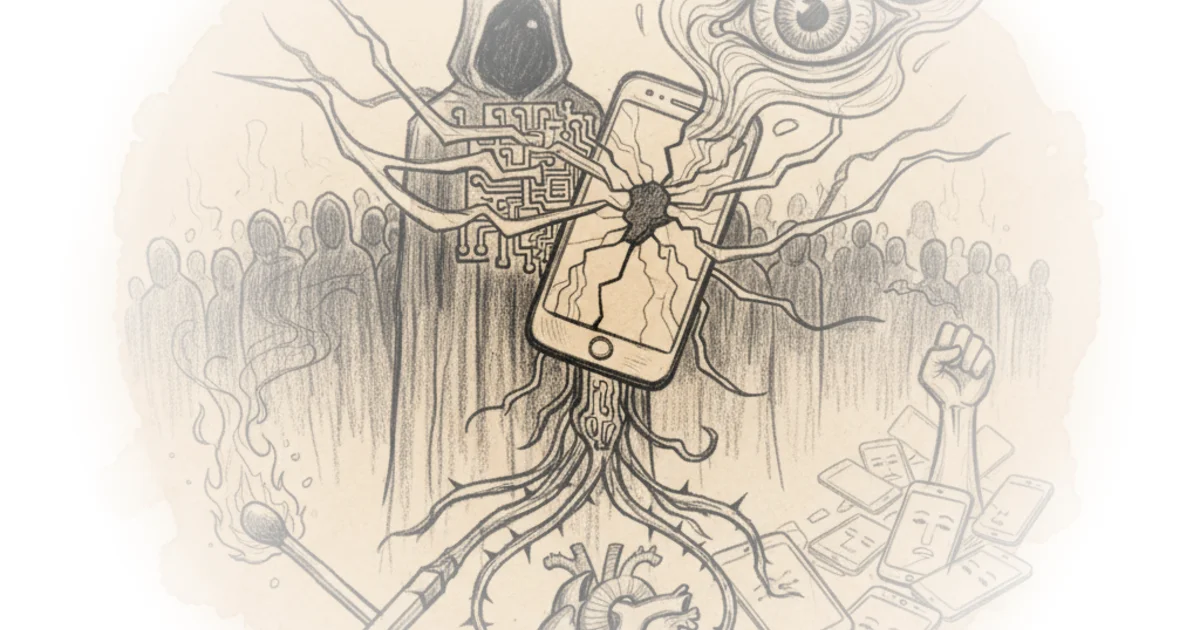
In an era where a single photograph can end a career, The Hated One argues that the most radical act of dissent is not shouting louder, but becoming invisible. This guide strips away the romanticism of protest to reveal a stark reality: modern law enforcement has evolved from physical suppression to digital erasure, turning every smartphone into a potential arrest warrant. For anyone considering taking to the streets, the author's central thesis is chillingly clear—surveillance is now the primary weapon against democracy, and the only defense is extreme, uncompromising anonymity.
The Digital Trap
The Hated One opens by dismantling the assumption that a smartphone is a neutral tool for documentation. Instead, they frame it as a beacon that broadcasts identity to anyone with the right equipment. "Surveillance is the most powerful tool to silence descent," the author writes, noting that police can now intercept radio signals to extract unique identifiers and trace them back to homes and offices without ever touching the device. This reframing is crucial; it shifts the conversation from physical safety to digital hygiene, arguing that resilience in the 21st century requires protecting one's data as fiercely as one's body.
The author details how cellular radios, Wi-Fi, and Bluetooth beacons act as constant trackers. "Your SIM card has a unique IMEI number that is broadcast indiscriminately into all directions," they explain, describing how "IMSI catchers" can capture this data to find real phone numbers and intercept communications. This is not theoretical paranoia but a description of standard police capability. The Hated One argues that because these signals are so revealing, the only safe option is to leave personal devices at home entirely.
Critics might note that the logistical difficulty of maintaining total digital silence could deter participation, potentially shrinking the movement rather than protecting it. However, the author insists that the risk of identification outweighs the convenience of connectivity.
The Burner Protocol
Moving to solutions, The Hated One provides a granular, almost technical manual for acquiring and using a "burner" device. They are unequivocal about what not to use: "iPhones cannot be used anonymously since an iPhone will not function properly without an Apple ID." They argue that Apple's ecosystem is too deeply integrated with personal identity data, which the government can request at any time. Instead, the author champions the Google Pixel running GrapheneOS, an open-source operating system that allows for complete isolation from Google's tracking infrastructure.
The guide outlines a rigorous acquisition process: purchasing a carrier-unlocked device with cash, avoiding any personal Google accounts, and installing the operating system before the device ever enters the user's home. "A burner phone is a single use or single purpose device... that only contains information relevant to the task and nothing more," The Hated One writes. This level of operational security is presented not as optional, but as a prerequisite for effective protest.
"Your goal must be to become unidentifiable."
The author's insistence on physical isolation is equally strict. They advise removing smartwatches and keeping tablets at home, noting that "every step suggested will be accompanied by a proper explanation to help you understand why you should follow it." This pedagogical approach suggests that the author views anonymity as a skill set that must be mastered, not just a gadget to buy. The recommendation to use Faraday bags to seal all radio signals when not in use further underscores the depth of the threat model.
Operational Security and Communication
Once the hardware is secured, The Hated One turns to software, advocating for a suite of open-source tools that route traffic through the Tor network. They recommend installing F-Droid, a repository for privacy-respecting apps, and using Orbot to create a secure tunnel for all internet traffic. "Tor is slower than clear internet access but it is faster than spending time in jail because it didn't protect your traffic," the author asserts, a pragmatic calculation that prioritizes long-term freedom over short-term convenience.
The guide also addresses the human element of security, advising protesters to create anonymous email addresses and store credentials in an encrypted database like KeePassDX. "Communication with your fellow protesters... has to be anonymous and encrypted even if you know each other," they warn, highlighting that trust within a group does not negate the need for technical safeguards. The author suggests that even metadata can be dangerous, urging users to disable biometric unlocking in favor of long alphanumeric passcodes to prevent forced unlocking by authorities.
A counterargument worth considering is that the complexity of this setup—requiring specific hardware, cash purchases, and technical knowledge—creates a barrier to entry that may exclude those without technical literacy or financial resources. The Hated One acknowledges this by offering a "least secure" option of factory-resetting a personal device, but maintains that it is a compromise that should be avoided if possible.
Bottom Line
The Hated One's guide is a masterclass in threat modeling, effectively arguing that in the current legal and technological landscape, the default state of a protestor is exposed. Its greatest strength is the refusal to offer half-measures, insisting that partial anonymity is no anonymity at all. However, its biggest vulnerability lies in its accessibility; the rigorous protocols described may be too demanding for the average citizen, potentially limiting its utility to a small cadre of highly skilled activists. The piece serves as a stark reminder that the battlefield of modern dissent has moved from the pavement to the server, and the rules of engagement have changed forever.