In an era where nine billion online accounts are already compromised, The Hated One delivers a sobering reality check: security is not a product you buy, but a process you live. The piece cuts through the noise of expensive software recommendations to argue that the most critical defense is a shift in mindset—from relying on passwords to mastering operational security. This is not just a tutorial; it is a manifesto for digital survival in a world where companies are often helpless and police are outmatched.
The Illusion of Safety
The Hated One opens with a staggering statistic that reframes the entire conversation: "at least nine billion online accounts have been compromised and there's just the lowest estimate of what is publicly available." This figure sets a tone of urgency, suggesting that the average user is already fighting a losing battle against a backdrop of systemic failure. The author argues that the legal and institutional frameworks are broken, noting that "when you get hacked the odds are you're gonna have hard time holding the company with weak security accountable."
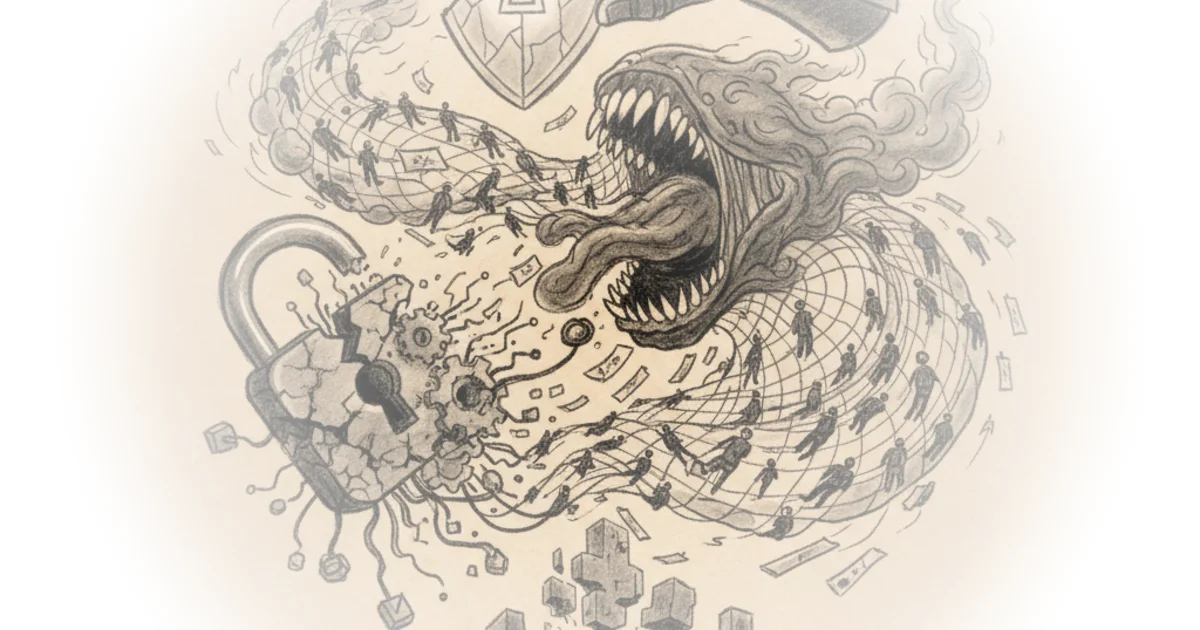
This framing is crucial because it removes the burden of perfection from the individual while simultaneously demanding vigilance. The Hated One posits that "nothing is unbreakable and there is no such thing as a hundred percent security," a statement that forces the reader to abandon the fantasy of a perfect shield. Instead, the focus shifts to limiting exposure and preparing for the inevitable breach.
Security is a process, not about the tools you can have strong passwords second factor authentication and the most expensive iPhone but what are you gonna do when you see this?
The argument here is that technical tools are useless without the human element of operational security. The author illustrates this with the example of phishing, where a "perfect clone made by a thief" can fool an untrained eye. The takeaway is stark: "if you have a bad OPSEC no tool can save you." This is a powerful, if somewhat fatalistic, stance. Critics might note that this places an immense cognitive load on users, expecting them to be constantly hyper-vigilant in a landscape designed to exploit human error. However, the author's insistence on this point is the piece's most valuable contribution, as it highlights that technology alone cannot solve a human problem.
Compartmentalization and the Password Fallacy
The core of the strategy proposed is "security by compartmentalization," or simply, not putting all your eggs in one basket. The Hated One explains that this mindset accepts that breaches will happen, so the goal is to ensure that "if attackers access one compartment it doesn't mean they can access all of your accounts and data in other compartments." This is a practical application of the "20% of effort needed to mitigate 80% of threats" principle.
To achieve this, the author advocates for a radical shift from passwords to passphrases. The text suggests creating a phrase that is "too long to brute-force and also make them unlikely to be in the dictionary," offering the example: "I'd roll along so ghosts penis 4:20 Yolo." While the example is intentionally bizarre, the principle holds: length and unpredictability are key. The Hated One writes, "the best way to create strong and unique passwords is to use a password manager," emphasizing that "any password manager is better than reusing your passwords."
The author goes further, recommending open-source alternatives like Bitwarden or KeePass to avoid "blindly trust[ing] any default options on our phone or browser." This distrust of corporate defaults is a recurring theme. The Hated One argues that companies "suck at their own security and under pay their own sis [security teams]," leading to inevitable breaches where "your carefully created password is out in the open." This cynical view of corporate security is well-supported by recent history, though it risks discouraging users who feel they have no control over the platforms they rely on.
The Human Firewall: Email and Social Engineering
Perhaps the most actionable advice in the piece concerns email management. The Hated One warns, "do not use the same email address for all your online accounts," explaining that if a hacker breaches one address, they can "reset your passwords to social media retail websites or possible even banking." The solution offered is compartmentalization via email aliases. The author cites a security expert who suggests using services that "give you the option to create loads of emails that will just forward everything to your real Yuma email address."
This strategy effectively isolates the user's primary identity from the vast web of online services. The Hated One notes that in password leaks, "you can just search for an email and you will get five to ten accounts," making it easy for attackers to pivot. By using aliases, the user makes this mapping nearly impossible.
Compartmentalize your online accounts with separate email addresses make them hard to guess as well emails that go with first name dot last name and email provider comm should only be used for official correspondence.
The piece also tackles the weak link of security questions, calling them a "terrible practice" because the answers are often found via social media. The Hated One suggests using a password manager to generate "gibberish answers to these questions that are impossible to guess." This is a clever workaround that acknowledges the flaw in the system while providing a practical fix.
The Final Barrier: Two-Factor Authentication
The commentary culminates in a strong defense of two-factor authentication (2FA), which the author calls "absolutely necessary." The Hated One distinguishes between SMS-based 2FA, which is "better than nothing but shouldn't be considered secure," and app-based or hardware-based methods. The recommendation is clear: use authenticator apps like Aegis OTP or hardware keys like YubiKey or Nitro Key.
The author highlights the superiority of hardware keys, noting that "security keys should be supported by to the Noda Google Twitter Dropbox github and Facebook." This trend toward FIDO/U2F standards is presented as the future, where "this type of authentication is likely going to replace passwords entirely." The advice to "not leave your authentication keys plugged into your device all the time" adds a layer of physical security that is often overlooked.
However, the piece acknowledges the complexity of recovery. If a user loses their 2FA device, they are locked out. The Hated One suggests encrypting backups and storing them on a flash drive "somewhere safe outside of the other main device." This introduces a new risk: if someone finds the backup, they can access the account. The author advises, "if they're included with a good password you could also just leave them on the device you're using but if that device dies and that's your only device and everything's gone again." This trade-off between convenience and security is the central tension of the entire piece.
Security is like a group immunity the more people around your secure the lower your chances of getting infected.
The Hated One concludes by framing security as a collective responsibility. If everyone around you is secure, the overall risk decreases. This is a compelling, community-oriented argument that moves beyond individual paranoia to a broader sense of digital hygiene.
Bottom Line
The Hated One's greatest strength is the refusal to offer a silver bullet, instead presenting a layered, realistic defense strategy that prioritizes mindset over software. The argument that "security is a process" is the piece's most enduring insight, forcing readers to accept that perfection is impossible but resilience is achievable. The biggest vulnerability of this approach is the sheer cognitive load it places on the user; maintaining compartmentalized emails, managing hardware keys, and constantly checking URLs is a full-time job for many. Nevertheless, in a world of nine billion compromised accounts, this rigorous, paranoid approach is not just advisable—it is essential.