Most people believe that hiding their online activity is as simple as flipping a switch or paying for a subscription. The Hated One dismantles this comforting illusion with a stark reality check: in the modern surveillance economy, your metadata is far more dangerous than your content, and standard tools like Virtual Private Networks are often a false sense of security.
The Metadata Trap
The piece opens by challenging the efficacy of the tools most users rely on daily. The Hated One writes, "during your regular browsing session there are anywhere between two to three thousand third-party trackers trying to snatch your data or attack your device with malware." This is not a minor inconvenience; it is a systemic feature of the current internet architecture. The author argues that even with a VPN, you are not anonymous because "your vpn provider knows exactly the same information about you that your isp does."
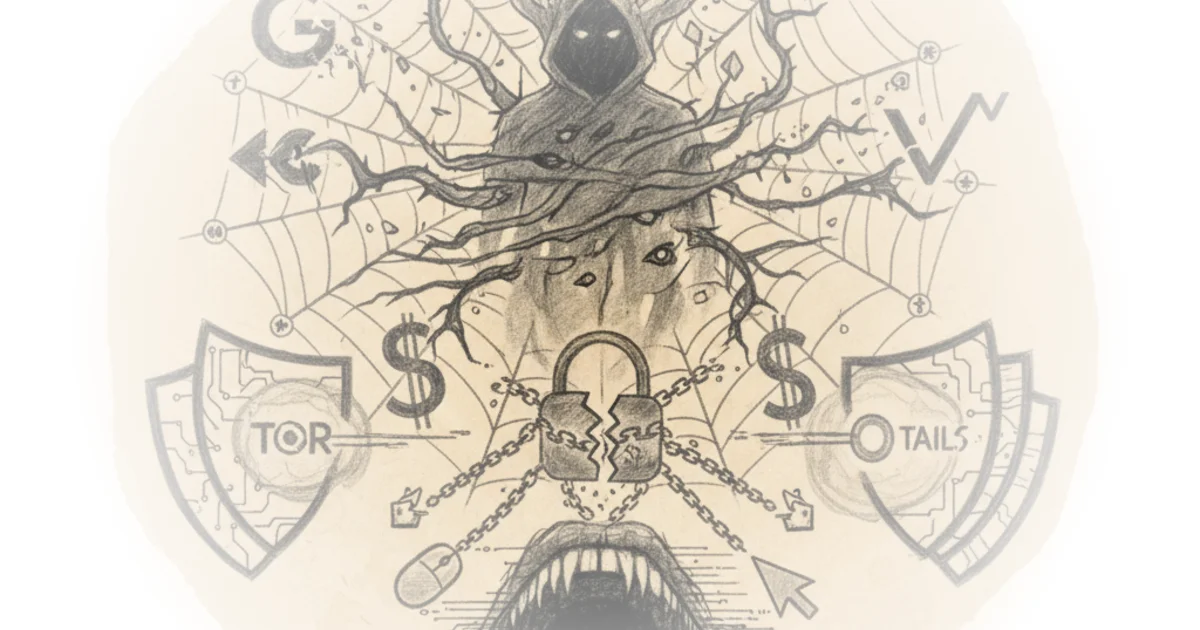
This distinction is crucial. While a VPN masks your location from your Internet Service Provider, it merely shifts the trust to the VPN provider, who still sees your traffic. The Hated One emphasizes that "modern trackers don't even need to know your ip address to track and know your identity." This reframes the problem from one of location to one of behavioral profiling. The stakes are raised significantly when the author points to the global trajectory of surveillance, noting that "it's only a matter of short time before these tools start being implemented in the west too."
Encryption only protects the content but in modern surveillance it's the metadata that's most valuable.
The commentary leans heavily on the idea that metadata—who you talk to, when, and for how long—is the real weapon. The Hated One quotes a former NSA official to drive this home: "okay we kill people based on metadata." This is a jarring, high-stakes claim that shifts the conversation from privacy to physical safety. While this specific quote refers to targeted killings, the underlying principle applies to the average user: your digital footprint can be weaponized for discrimination, social scoring, or loss of liberty. Critics might argue that the leap from targeted killing to social media tracking is a fear-mongering exaggeration, yet the mechanism of data aggregation remains identical regardless of the ultimate consequence.
The Tor Solution and Its Limits
Moving from the problem to the solution, the author introduces the Tor network. The Hated One explains that Tor achieves anonymity by "encrypting and rerouting your traffic through three independent tor relays or hops," ensuring that "none of the relays knows the full length of the tor traffic." This technical explanation is vital because it clarifies why Tor is fundamentally different from a VPN. However, the author is quick to temper expectations, warning that "just because they use tor you" don't get privacy if you log into accounts like Facebook.
The Hated One stresses that "you are not anonymous just for being on the tor network if you give someone your name." This is a critical behavioral insight. The technology is sound, but human error compromises it. The author advises users to "never sign in to online accounts on tor" and to avoid changing browser settings, as "if you make changes to how you look you're making yourself stand out." This highlights a paradox of anonymity: to be invisible, you must look exactly like everyone else. The advice to "never go full screen" and to "write your text in a text editor and then copy paste it" into a website is a testament to the depth of the threat model, where even keystroke dynamics and window size can be used for fingerprinting.
Operating System as the Final Frontier
The final and most demanding layer of the argument addresses the operating system itself. The Hated One posits that "tor browser is only as secure as the operating system you are running it on," which is why they advocate for Whonix, a Linux-based system designed to run inside a virtual machine. The author argues that this setup creates a "verifiably untraceable system" where even if malware escapes the browser, it is trapped within the virtual machine and cannot access the host system's real IP address.
This section moves beyond simple software recommendations to a philosophical stance on control. The Hated One writes, "using windows and macos is not secure because these platforms are not transparent about what they can and can't do with your data." The argument is that proprietary operating systems like Windows and macOS are inherently untrustworthy because "both apple and microsoft have been secret nsa partners for years and have built in backdoors into their systems." While this claim about backdoors is a subject of intense debate and often lacks public, verifiable proof for specific modern implementations, it reflects a deep-seated distrust of corporate control over user devices.
The author suggests migrating to open-source alternatives like PureOS or Linux Mint, stating that "if you tweak some settings on linux you can rest assured they will remain that way and they won't be reset remotely by a company." This is a powerful argument for digital sovereignty. The Hated One concludes that "the more people use linux the more diverse and the more secure the whole network becomes," framing the adoption of open-source software not just as a personal security measure, but as a civic duty to improve the internet ecosystem.
You are not in full control of your device if you run either of the operating systems and you can never trust their security and privacy layouts.
Critics might note that the barrier to entry for setting up Whonix and managing Linux virtual machines is prohibitively high for the average user, potentially limiting the practical impact of this advice to a small, tech-savvy elite. However, the author acknowledges this difficulty, admitting that "linux is something that will be in your way for a while but it is a habit and just like with anything it will become seamless after a while."
Bottom Line
The Hated One's most compelling contribution is the shift from viewing privacy as a feature of a browser to viewing it as a holistic system architecture that requires total control over the operating environment. The piece's greatest vulnerability lies in its absolute dismissal of proprietary systems, which may alienate readers who need to use standard corporate tools, but its core thesis—that true anonymity requires eliminating the attack surface of your host machine—remains a rigorous and necessary standard for anyone serious about digital safety.